Access control policy advanced settings
Advanced access control policy settings typically require little or no modification. The default settings are appropriate for most deployments. Note that many of the advanced preprocessing and performance options in access control policies may be modified by rule updates as described in Update Intrusion Rules.
If View ( ) appears instead, settings are inherited from an ancestor
policy, or you do not have permission to modify the
settings.
) appears instead, settings are inherited from an ancestor
policy, or you do not have permission to modify the
settings.
Caution | See Configurations that Restart the Snort Process When Deployed or Activated for a list of advanced setting modifications that restart the Snort process, temporarily interrupting traffic inspection. Whether traffic drops during this interruption or passes without further inspection depends on how the assigned device handles traffic. See Snort Restart Traffic Behavior for more information. |
Inheriting settings from a parent policy
If the access control policy has a base policy, you can elect to inherit settings from the base policy. Select Inherit from (base policy) for each setting group where you want to use the parent policy's settings. If inheritance has been configured so that these settings are locked, you cannot configure unique settings for the policy, these settings are read-only.
If you are allowed to configure unique settings for the policy, you must deselect the option to make your edits.
General settings
|
Option |
Description |
|---|---|
|
Maximum URL characters to store in connection events |
To customize the number of characters you store for each URL requested by your users. |
|
Allow an Interactive Block to bypass blocking for (seconds) |
To customize the length of time before you re-block a website after a user bypasses an initial block, see Setting the User Bypass Timeout for a Blocked Website. |
|
Retry URL cache miss lookup |
The first time the system encounters a URL that does not have a locally stored category and reputation, it looks up that URL in the cloud and adds the result to the local data store, for faster processing of that URL in the future. This setting determines what the system does when it needs to look up a URL's category and reputation in the cloud. By default, this setting is enabled: The system momentarily delays the traffic while it checks the cloud for the URL's reputation and category, and uses the cloud verdict to handle the traffic. If you disable this setting: When the system encounters a URL that is not in its local cache, the traffic is immediately passed and handled according to the rules configured for Uncategorized and reputationless traffic. In passive deployments, the system does not retry the lookup, as it cannot hold packets. |
| Enable Threat Intelligence Director |
Disable this option to stop publishing TID data to your configured devices. |
|
Enable reputation enforcement on DNS traffic |
This option is enabled by default, for improved URL filtering performance and efficacy. For details and additional instructions, see DNS Filtering: Identify URL Reputation and Category During DNS Lookup (Beta) and subtopics. |
|
Inspect traffic during policy apply |
To inspect traffic when you deploy configuration changes unless specific configurations require restarting the Snort process, ensure that Inspect traffic during policy apply is set to its default value (enabled). When this option is enabled, resource demands could result in a small number of packets dropping without inspection. Additionally, deploying some configurations restarts the Snort process, which interrupts traffic inspection. Whether traffic drops during this interruption or passes without further inspection depends on how the assigned device handles traffic. See Snort Restart Scenarios for more information. |
Associated policies
Use advanced settings to associate subpolicies (decryption, identity, prefilter) with access control; see Associating other policies with access control.
TLS server identity discovery
The latest version of the Transport Layer Security (TLS) protocol 1.3, defined by RFC 8446, is the preferred protocol for many web servers to provide secure communications. Because the TLS 1.3 protocol encrypts the server's certificate for additional security, and the certificate is needed to match application and URL filtering criteria in access control rules, the Firepower System provides a way to extract the server certificate without decrypting the entire packet.
You can enable this feature, referred to as TLS server identity discovery, when you configure advanced settings for an access control policy. Certain features are not supported, such as STARTTLS traffic, the HTTP CONNECT method, and in a network where another device is already decrypting traffic.
When a new connection starts that will be affected by TLS server identity discovery, the Firewall Threat Defense holds the original ClientHello packet to determine the identity of the server to which it connects before continuing. The Firewall Threat Defense device sends a specialized connection from the Firewall Threat Defense to the server. The server's response includes the server certificate, the specialized connection is terminated, and the original connection is evaluated as required by the access control policy.
TLS server identity discovery prioritizes the certificate's Common Name (CN) over the Server Name Indication (SNI).
To enable TLS server identity discovery, click the Advanced tab, click Edit ( ) for the setting, and select Early application detection and URL categorization.
) for the setting, and select Early application detection and URL categorization.
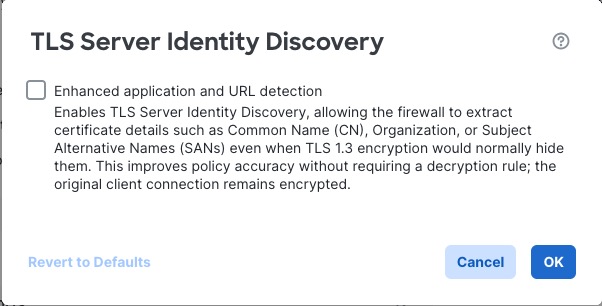
We strongly recommend enabling it for any traffic you want to match on application or URL criteria, especially if you want to perform deep inspection of that traffic. An SSL policy is not required because traffic is not decrypted in the process of extracting the server certificate.
Note |
|
Network analysis and intrusion policies
Advanced network analysis and intrusion policy settings allow you to:
-
Specify the intrusion policy and associated variable set that are used to inspect packets that must pass before the system can determine exactly how to inspect that traffic.
-
Change the access control policy’s default network analysis policy, which governs many preprocessing options.
-
Use custom network analysis rules and network analysis policies to tailor preprocessing options to specific security zones, networks, and VLANs.
For more information, see Advanced Access Control Settings for Network Analysis and Intrusion Policies.
Threat Defense service policy
You can use the Threat Defense service policy to apply services to specific traffic classes. For example, you can use a service policy to create a timeout configuration that is specific to a particular TCP application, as opposed to one that applies to all TCP applications. This policy applies to devices only, and will be ignored for any other device type. The service policy rules are applied after the access control rules. For more information, see Service Policies.
File and malware settings
Tuning File and Malware Inspection Performance and Storage provides information on performance options for file control and malware defense.
Intelligent application bypass settings
Intelligent application bypass (IAB) is an expert-level configuration that specifies applications to bypass or test for bypass if traffic exceeds a combination of inspection performance and flow thresholds.
IAB settings are applicable for Snort2 devices or pre 7.2.0 Snort3 devices. For more information, see Intelligent Application Bypass.
Transport/network layer preprocessor settings
Advanced transport and network preprocessor settings apply globally to all networks, zones, and VLANs where you deploy your access control policy.
-
Ignore the VLAN header when tracking connections —Different VLAN tags in traffic traveling in different directions for the same connection can affect traffic reassembly and rule processing. For example, traffic for the same connection could be transmitted over VLAN A and be received over VLAN B. Select this option to configure the system to ignore the VLAN header so packets can be correctly processed for your deployment.
-
Maximum Active Responses—For a TCP connection that triggers a preprocessor/intrusion rule that is configured to provide an active response, the maximum number of active responses per TCP connection. When additional traffic occurs on a connection where an active response has been initiated, and the traffic occurs more than Minimum Response Seconds after a previous active response, the system sends another active response unless the specified maximum has been reached. A setting of 0 disables additional active responses triggered active response rules.
-
Minimum Response Seconds—Until Maximum Active Responses occur, specifies the number of seconds to wait before any additional traffic on a connection where the system has initiated an active response results in a subsequent active response.
-
Session Termination Logging Threshold—Do not modify this option unless instructed to do so by Cisco Technical Support. This option specifies for the number of bytes that result in a logged message when the session terminates and the specified number was exceeded. Changing the option can affect system performance.
Detection enhancement settings
Detection enhancement settings determine whether adaptive profiles are used for application detection and intrusion rules in the access control policy. Typically, the system uses the static settings in your network analysis policy to preprocess and analyze traffic. With adaptive profile updates, the system can adapt processing behavior using host information either detected by network discovery or imported from a third party.
To enable adaptive profiles in Snort 3, you must select both the Enable and Enable Profile Updates options.
-
Enable—You must enable adaptive profiling (its default state) for access control rules to perform application and file control, including malware protection (AMP), and for intrusion rules to use service metadata.
-
Enable Profile Updates—Profile updates, like the target-based profiles you can configure manually in a network analysis policy, help to defragment IP packets and reassemble streams in the same way as the operating system on the target host. The intrusion rules engine then analyzes the data in the same format as that used by the destination host. Profile updates also compare metadata in an intrusion rule to host information to determine whether a rule should apply for a particular host.
-
Adaptive Profiles – Attribute Update Interval—When profile updates are enabled, you can control how frequently in minutes network map data is synced from the management center to its managed devices. The system uses the data to determine what profiles should be used when processing traffic. Increasing the value for this option can improve performance in a large network.
-
Adaptive Profiles – Networks—Optionally, when profile updates are enabled, you can improve performance by constraining profile updates to a comma-separated list of IP addresses, address blocks, and network variables. If you use a network variable, the system uses the variable's value in the variable set linked to the default intrusion policy for your access control policy. For example, you could enter: 192.168.1.101, 192.168.4.0/24, $HOME_NET. IPv4 and IPv6 are supported.
The default value (0.0.0.0/0) applies adaptive profile updates to all networks.
Performance settings and latency-based performance settings
About Intrusion Prevention Performance Tuning provides information on improving the performance of your system as it analyzes traffic for attempted intrusions.
For information specific to latency-based performance settings, see Packet and Intrusion Rule Latency Threshold Configuration.
Experimental features
Experimental features are those that are being tested in active networks to obtain real-world results. These features might not work as expected. When you enable an experimental feature, verify your actual results with the expected behavior.
-
Encrypted Visibility Engine—This is an experimental feature for FMC 7.1.0. For details about this feature, see the Encrypted Visibility Engine chapter in the Cisco Secure Firewall Management Center Snort 3 Configuration Guide.